Enable SSO with Azure Active Directory (OIDC)
Firezone supports Single Sign-On (SSO) using Azure Active Directory through the generic generic OIDC connector. This guide will walk you through how to obtain the following config settings required for the integration:
- Config ID: The provider's config ID. (e.g.
azure) - Label: The button label text that shows up on your Firezone login screen.
(e.g.
Azure) - Scope:
OIDC scopes
to obtain from your OIDC provider. This should be set to
openid email profile offline_accessto provide Firezone with the user's email in the returned claims. - Response type: Set to
code. - Client ID: The client ID of the application.
- Client secret: The client secret of the application.
- Discovery Document URI: The OpenID Connect provider configuration URI which returns a JSON document used to construct subsequent requests to this OIDC provider.
Step 1: Obtain configuration parameters
This guide is adapted from the Azure Active Directory documentation.
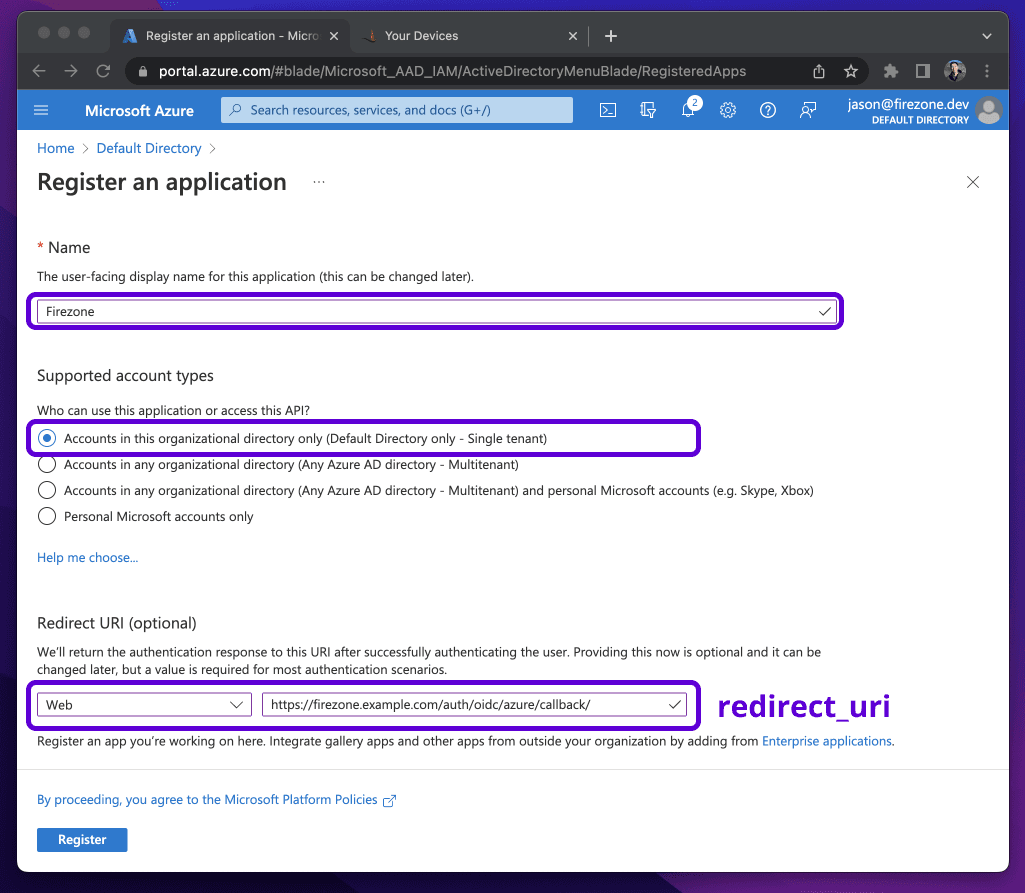
Navigate to the Azure Active Directory page on the Azure portal. Select the App
registrations link under the Manage menu, click New Registration, and register
after entering the following:
- Name:
Firezone - Supported account types:
(Default Directory only - Single tenant) - Redirect URI: This should be your Firezone
EXTERNAL_URL + /auth/oidc/<Config ID>/callback/(e.g.https://firezone.example.com/auth/oidc/azure/callback/). Make sure you include the trailing slash both when saving the provider in Firezone and in Azure AD (redirect_urifield on the screenshot below).
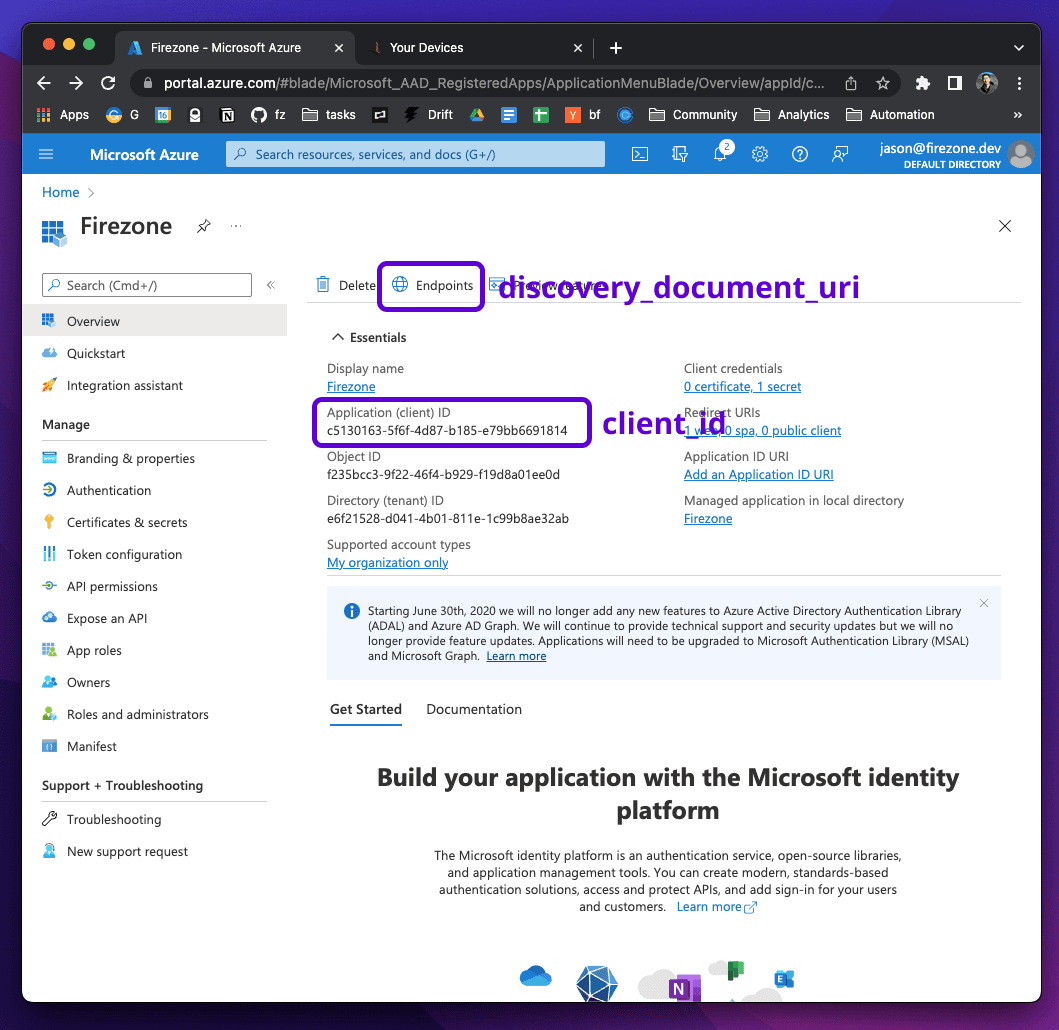
After registering, open the details view of the application and copy the
Application (client) ID. This will be the client_id value. Next, open
the endpoints menu to retrieve the OpenID Connect metadata document. This
will be the discovery_document_uri value.
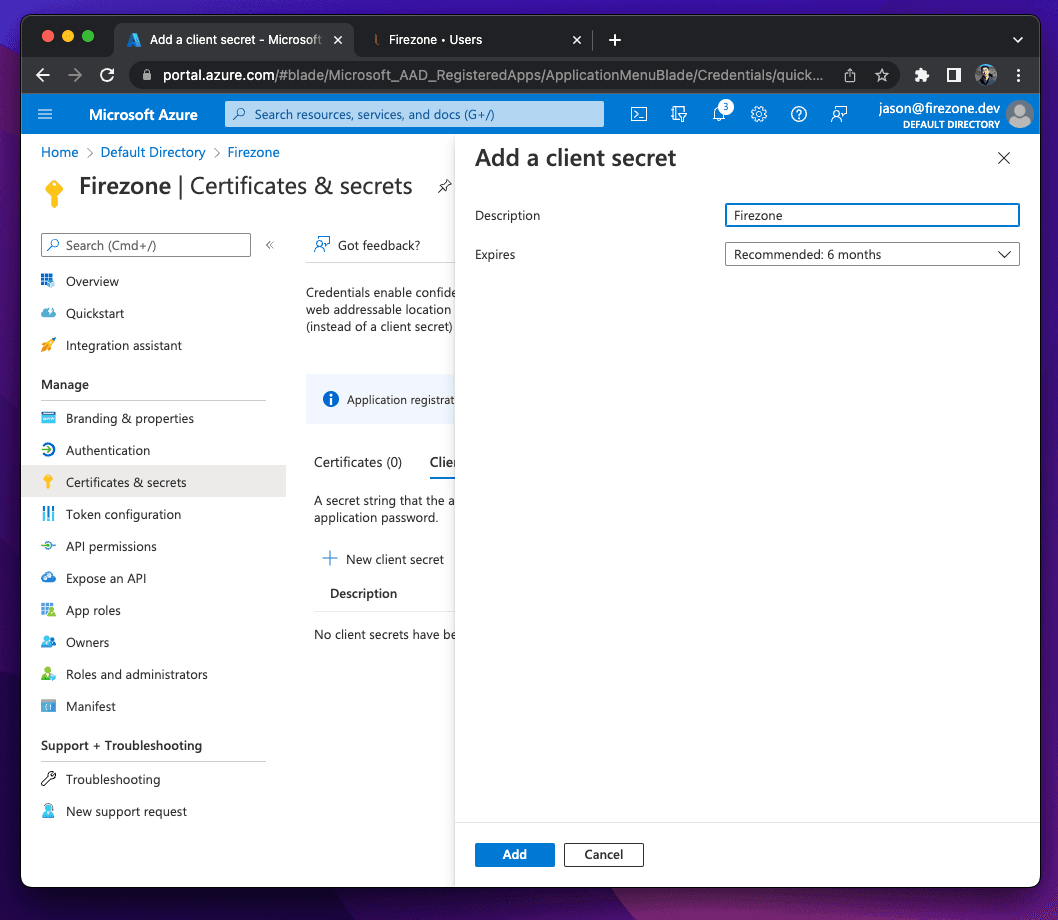
Next, select the Certificates & secrets link under the Manage menu and create a
new client secret. Copy the client secret - this will be the client_secret
value.
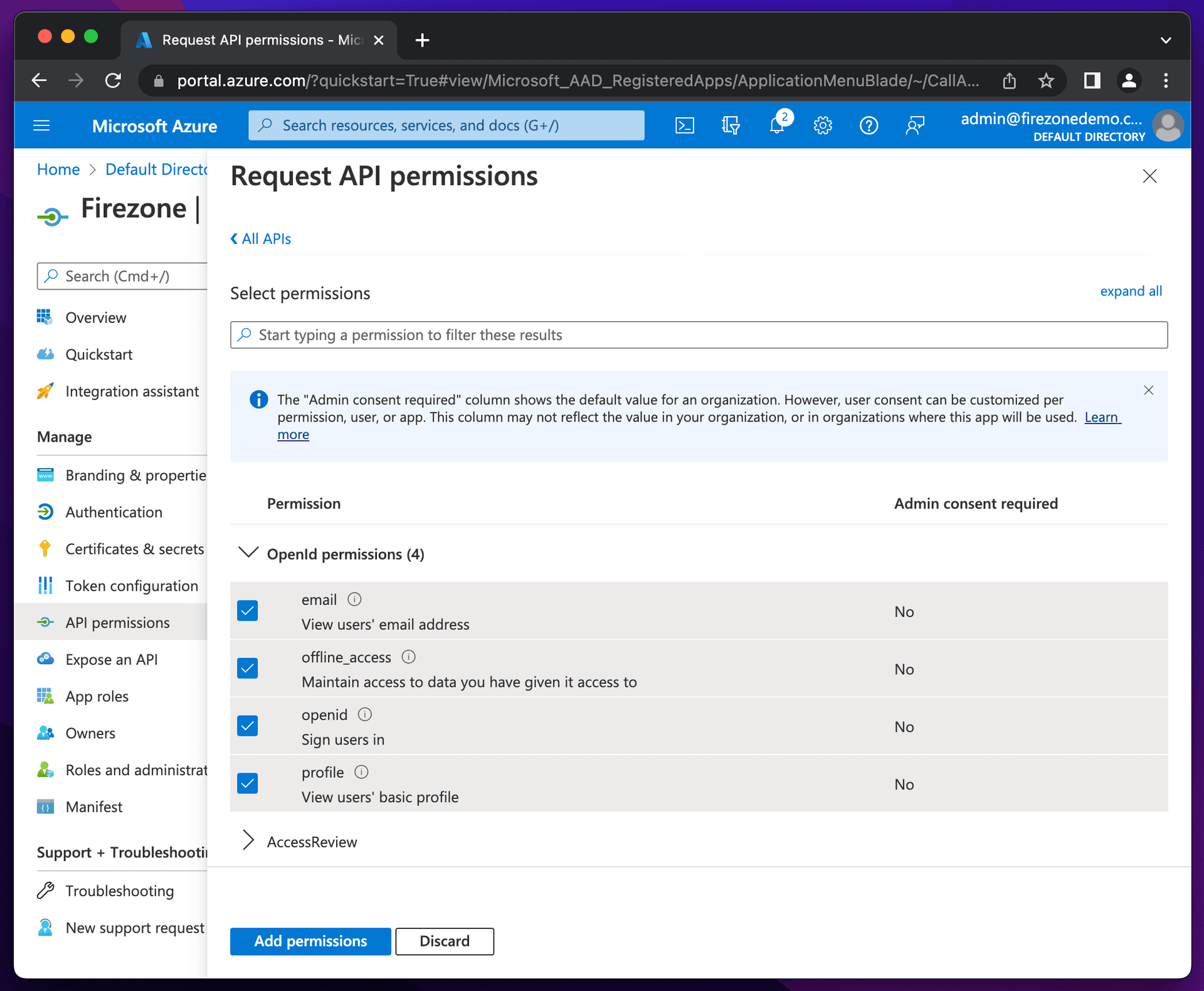
Lastly, select the API permissions link under the Manage menu, click
Add a permission, and select Microsoft Graph. Add email, openid,
offline_access and profile to the required permissions.
Step 2: Integrate with Firezone
Navigate to the /settings/security page in the admin portal, click "Add OpenID
Connect Provider" and enter the details you obtained in the steps above.
Enable or disable the Auto create users option to automatically create an unprivileged user when signing in via this authentication mechanism.
And that's it! The configuration should be updated immediately. You should now
see a Sign in with Azure button on the sign in page.
Step 3 (optional): Restrict access to specific users
Azure AD allows admins to restrict OAuth application access to a subset of users within your organization. See Microsoft's documentation for more information on how to do this.